Configuring the Azure web app using REST API
Some types of Azure configuration cannot be done from the Azure portal and require the use of the config update REST API.
While any of the available settings can be configured using the config update API, let's take the example of configuring the TLS Cipher Suites, in particular, setting the minimum cipher level for an Azure web app.
To do this, follow these steps:
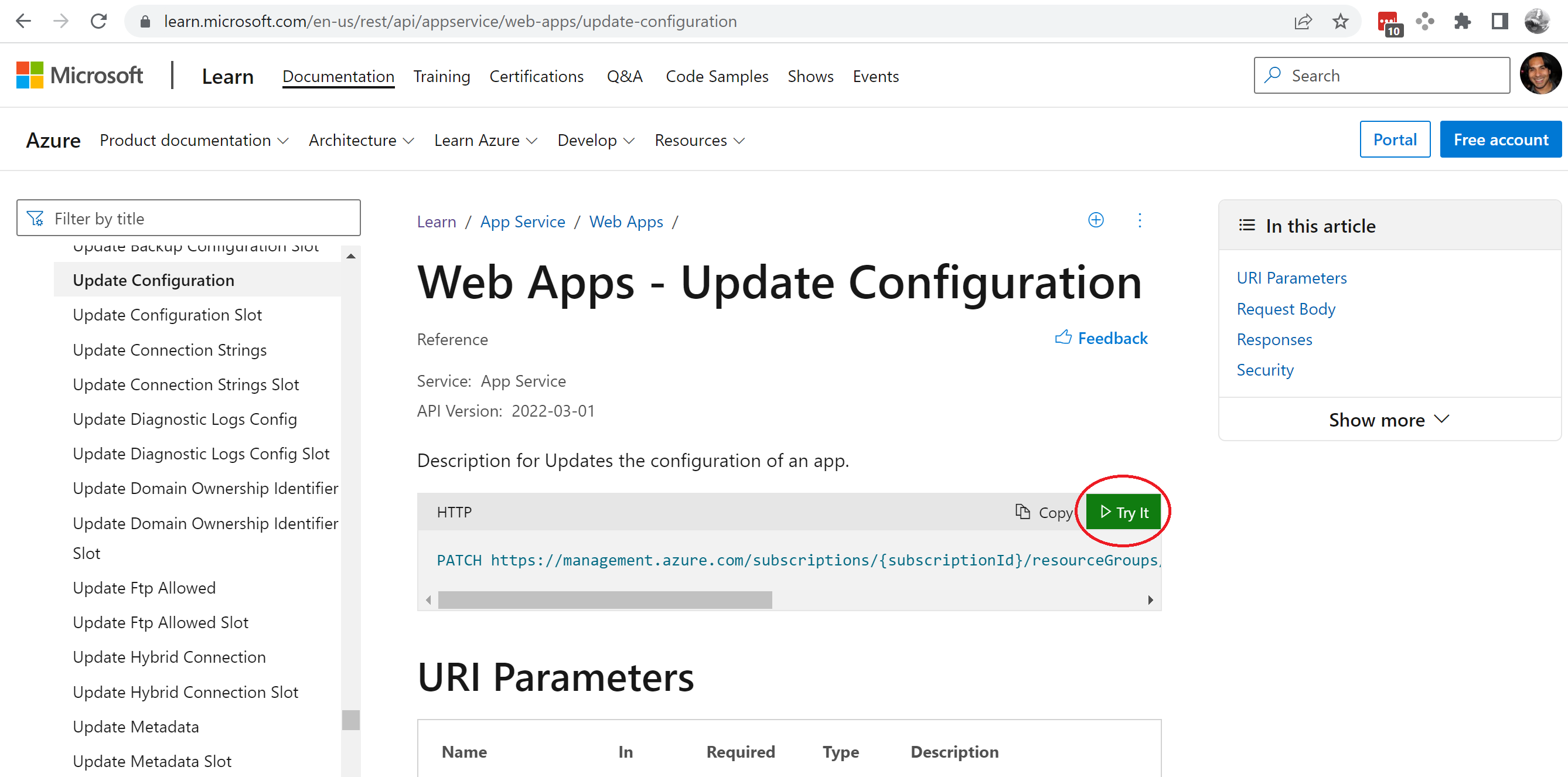
- Go to the following link - https://learn.microsoft.com/en-us/rest/api/appservice/web-apps/update-configuration
- Click on the button with the label, "Try it".
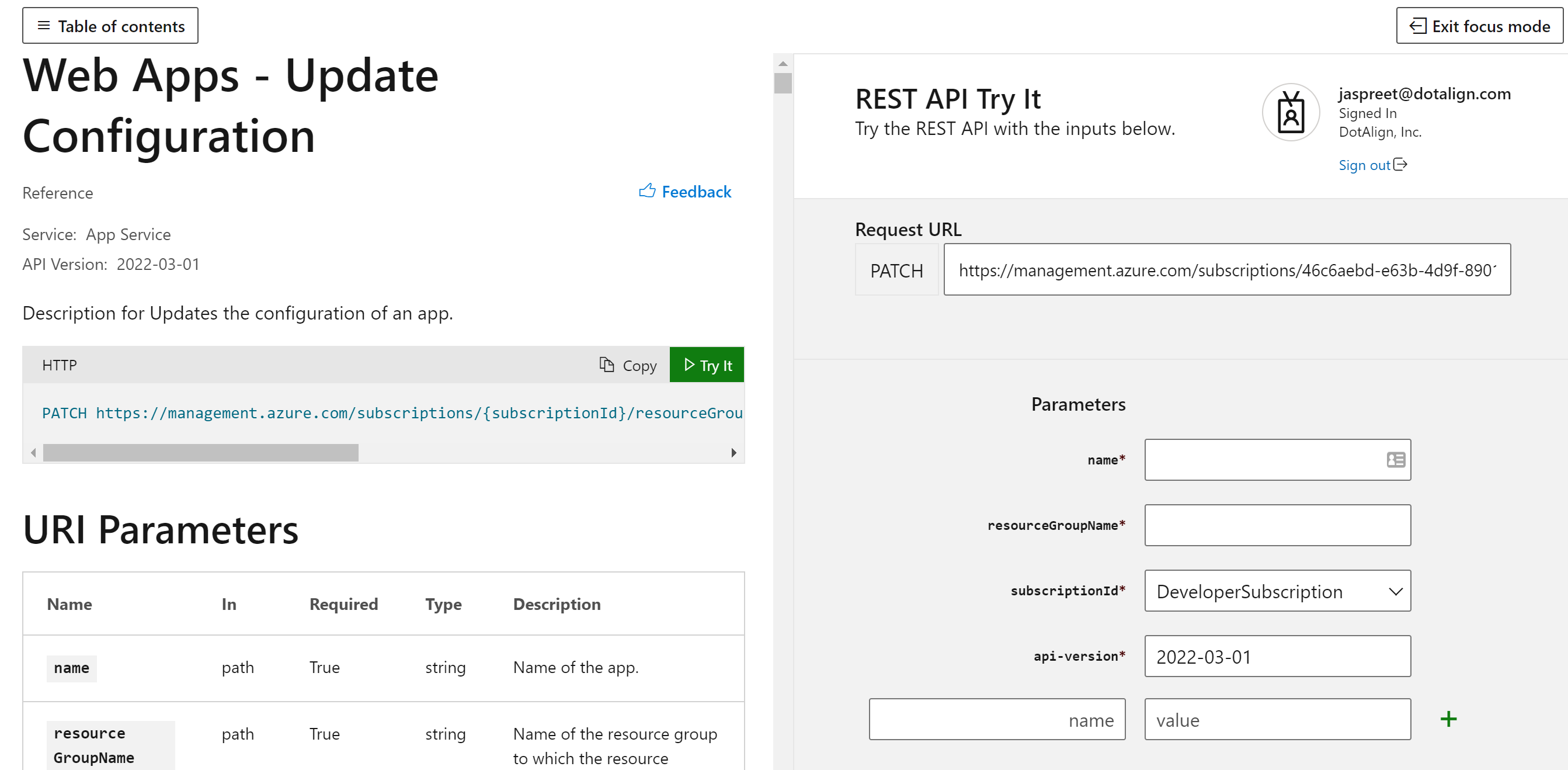
- Clicking on the "Try it" button will open up an area of the page where you can first authenticate and set up the parameters for executing specific requests using the config API.
- The supported TLS cipher levels available are as follows, in decreasing level of complexity. Further more, the ones with the prefix
TLS_RSA_WITH_AESare static key ciphers are are often flagged as a security risk.
TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384,
TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256,
TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256,
TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384,
TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256,
TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384,
TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256,
TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA,
TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA,
TLS_RSA_WITH_AES_256_GCM_SHA384,
TLS_RSA_WITH_AES_128_GCM_SHA256,
TLS_RSA_WITH_AES_256_CBC_SHA256,
TLS_RSA_WITH_AES_128_CBC_SHA256,
TLS_RSA_WITH_AES_256_CBC_SHA,
TLS_RSA_WITH_AES_128_CBC_SHA
To configure the web app to use cipher level TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 or above, we need to make a POST request to the config update API with the following body.
{
"properties": {
"minTlsCipherSuite": "TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384"
}
}You must also fill out the web app name, resource group name and choose the right subscription. The filled out form will look like below.
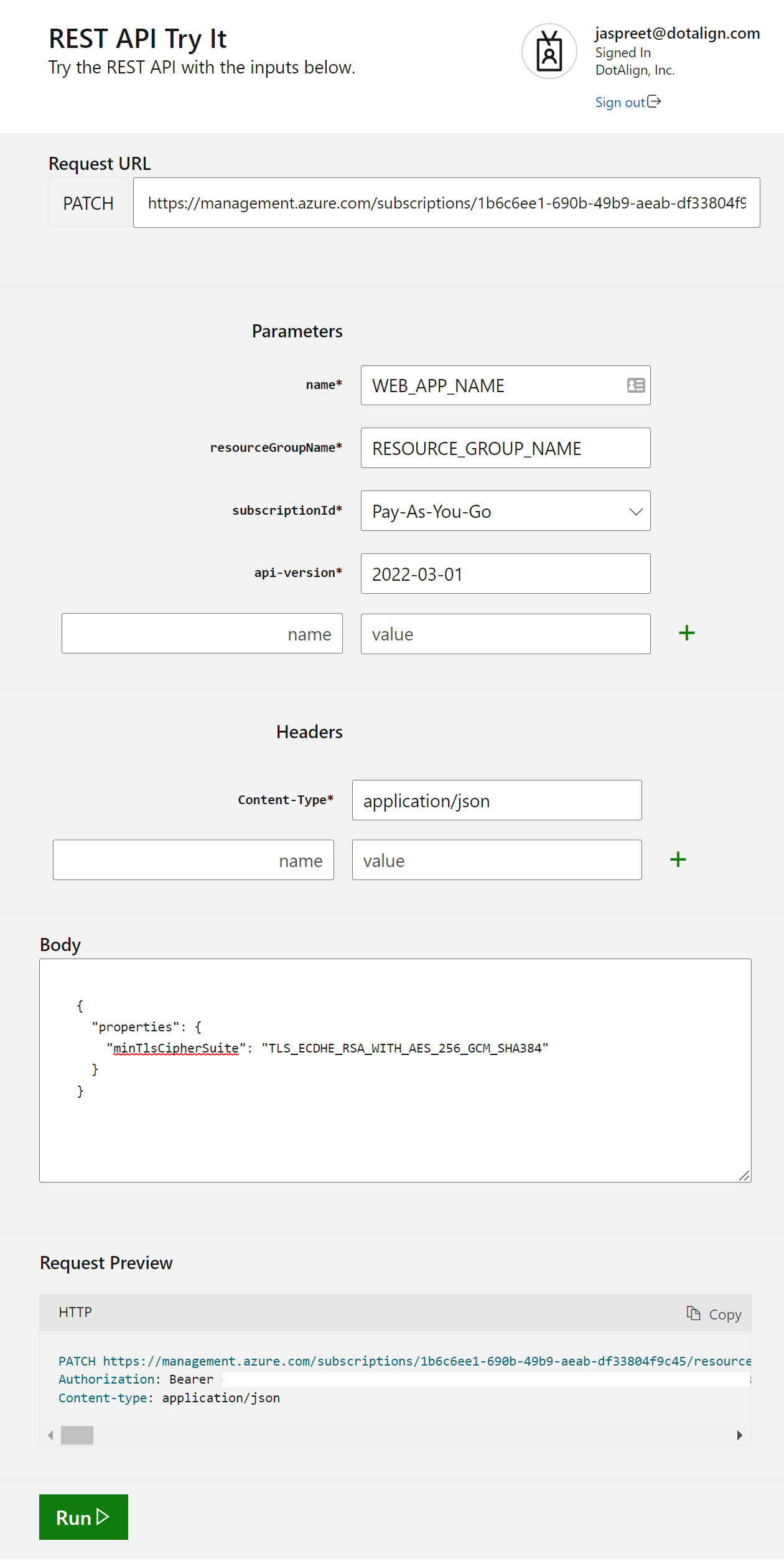
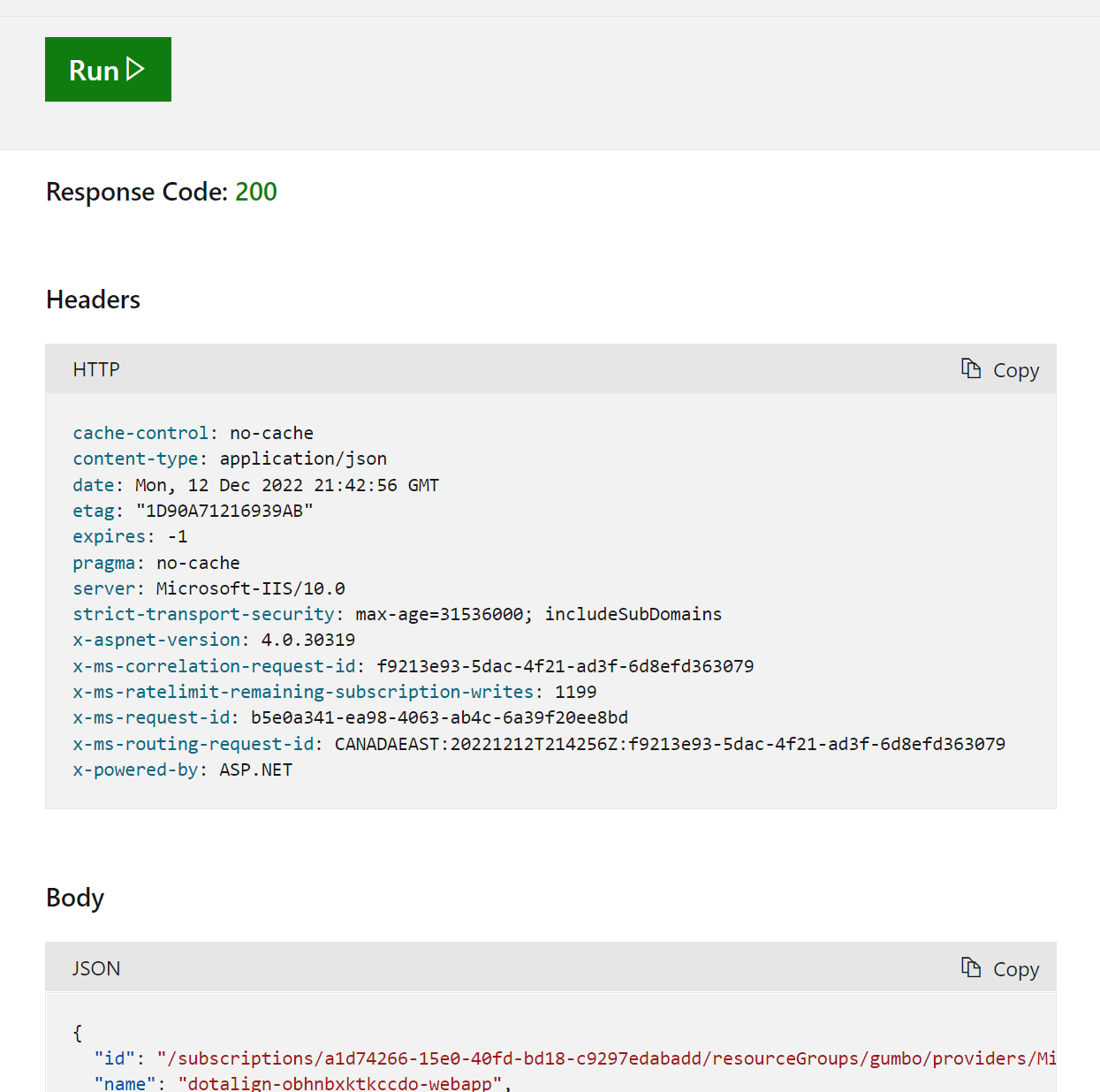
- Click on the "Run" button and ensure that the return code is 200, and that
minTlsCipherSuitehas been correctly set in the response body.